Decision Engine
This application allows the creation of various models for simple decision flows or complicated calculations and scoring options.
Powerful features
Our goal is simple - we aim to give financial service providers more time to focus on customers and growth while keeping costs low and reducing risk.
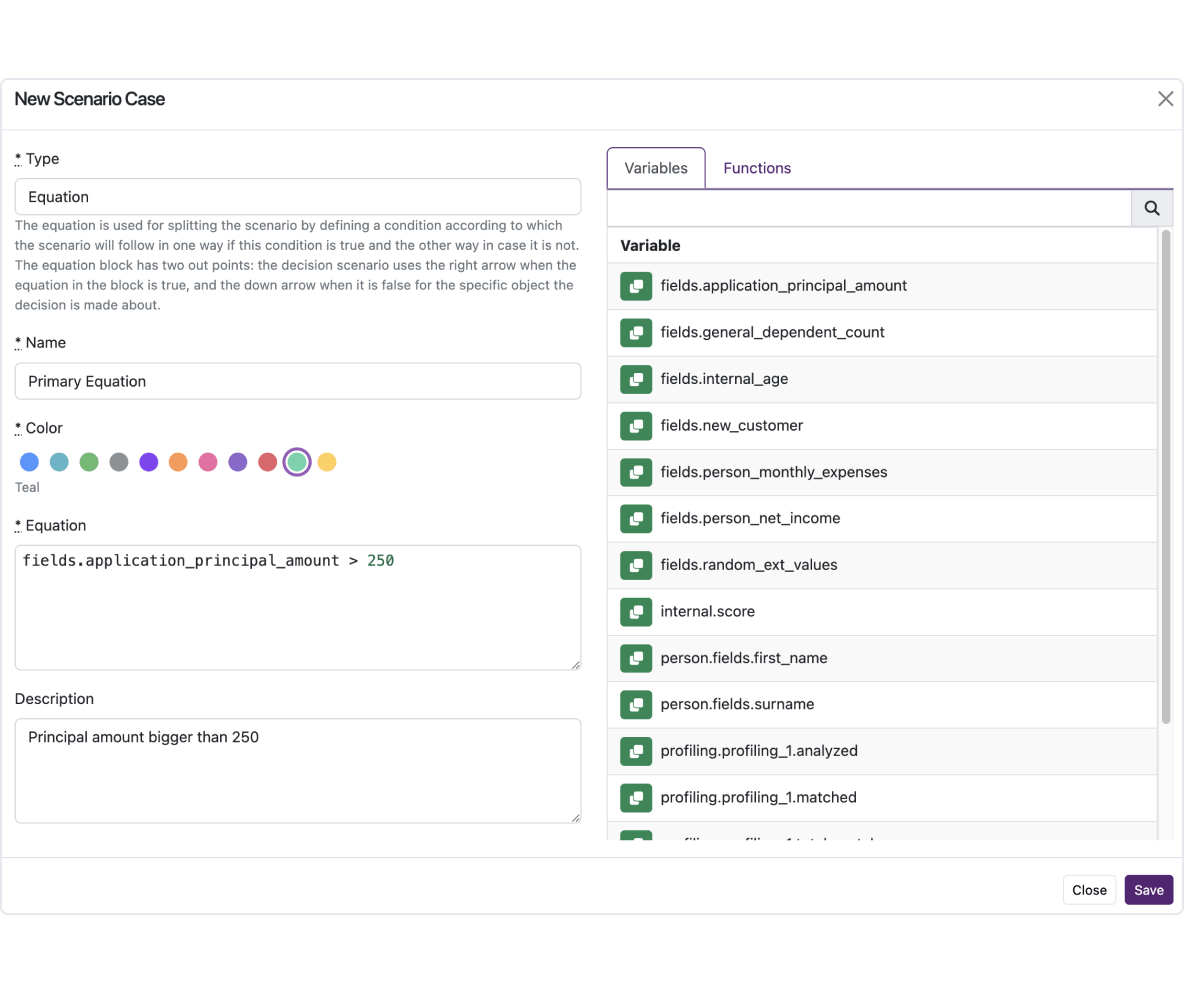
Inputs and equations
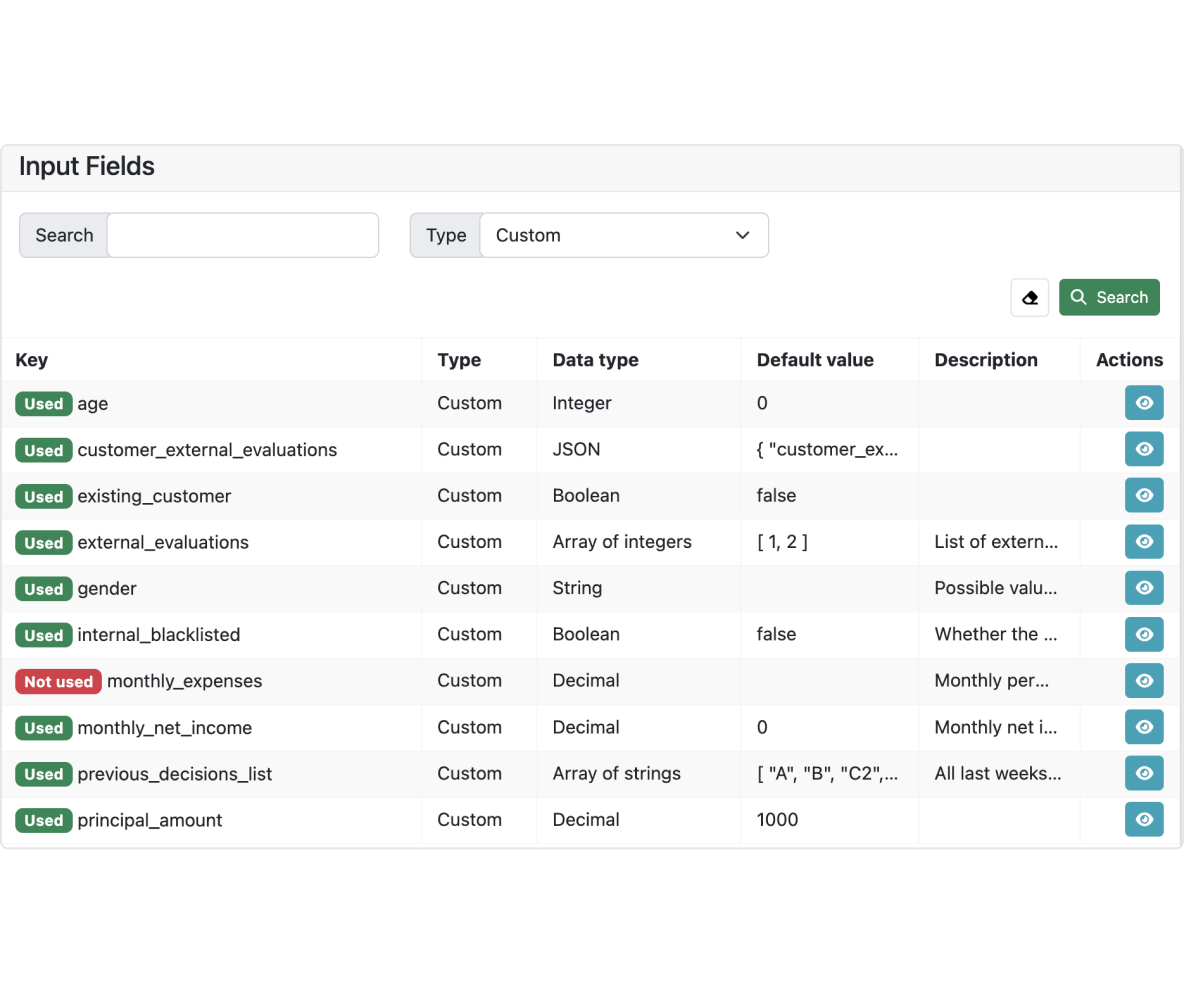
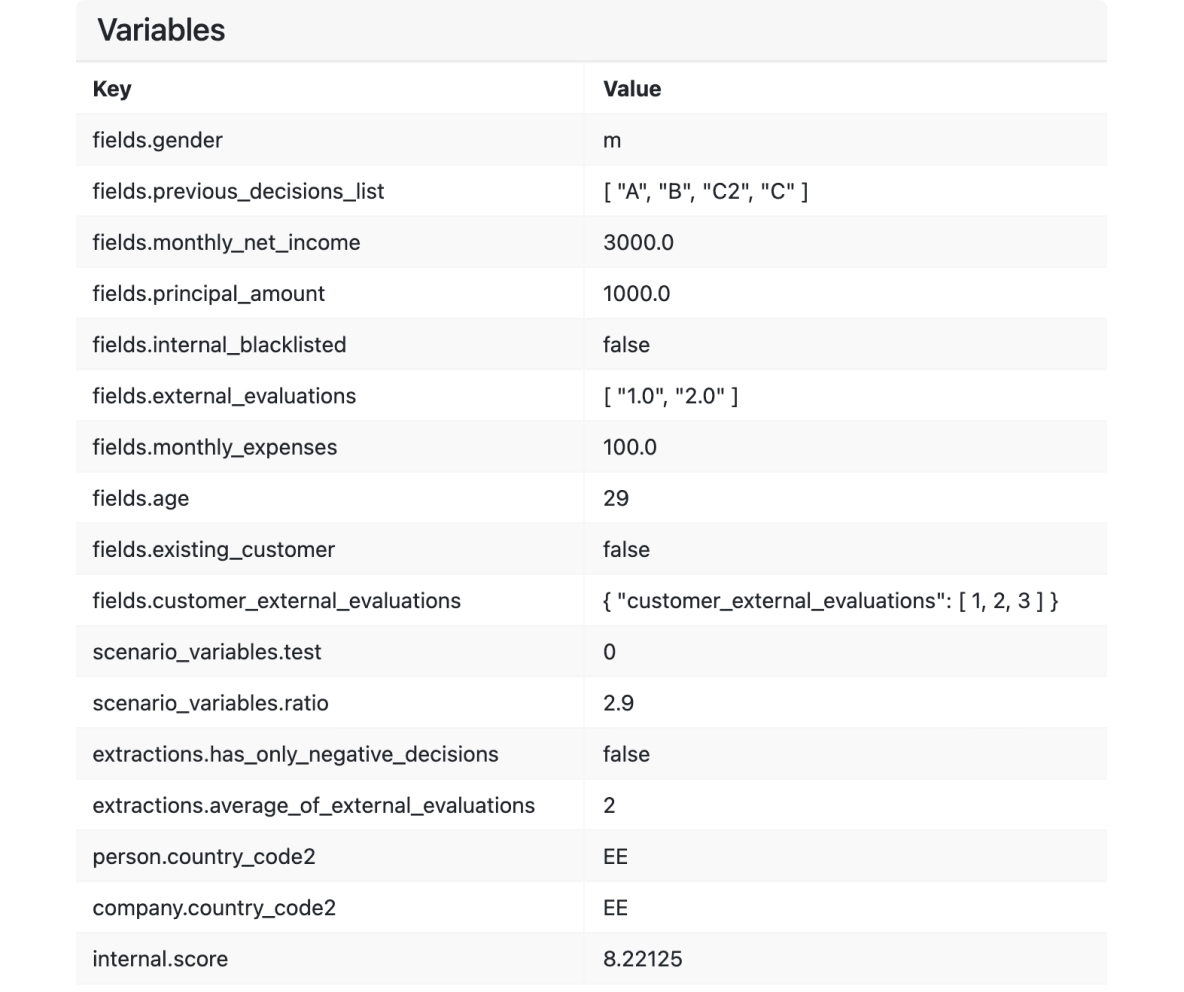
The creation of instant decision-making models is streamlined through the use of input information and equations. Define the necessary data for your model, sourced from integrated providers, customer histories, or other relevant sources.
- Customizable data fields: Easily add customizable fields that align with your existing system and perform calculations using tailored financial formulas, incorporating these data fields and a comprehensive set of variables to accurately quantify risks.
- Core system integration: If you're using our Core system, create data fields with corresponding key values to have them available across the platform.
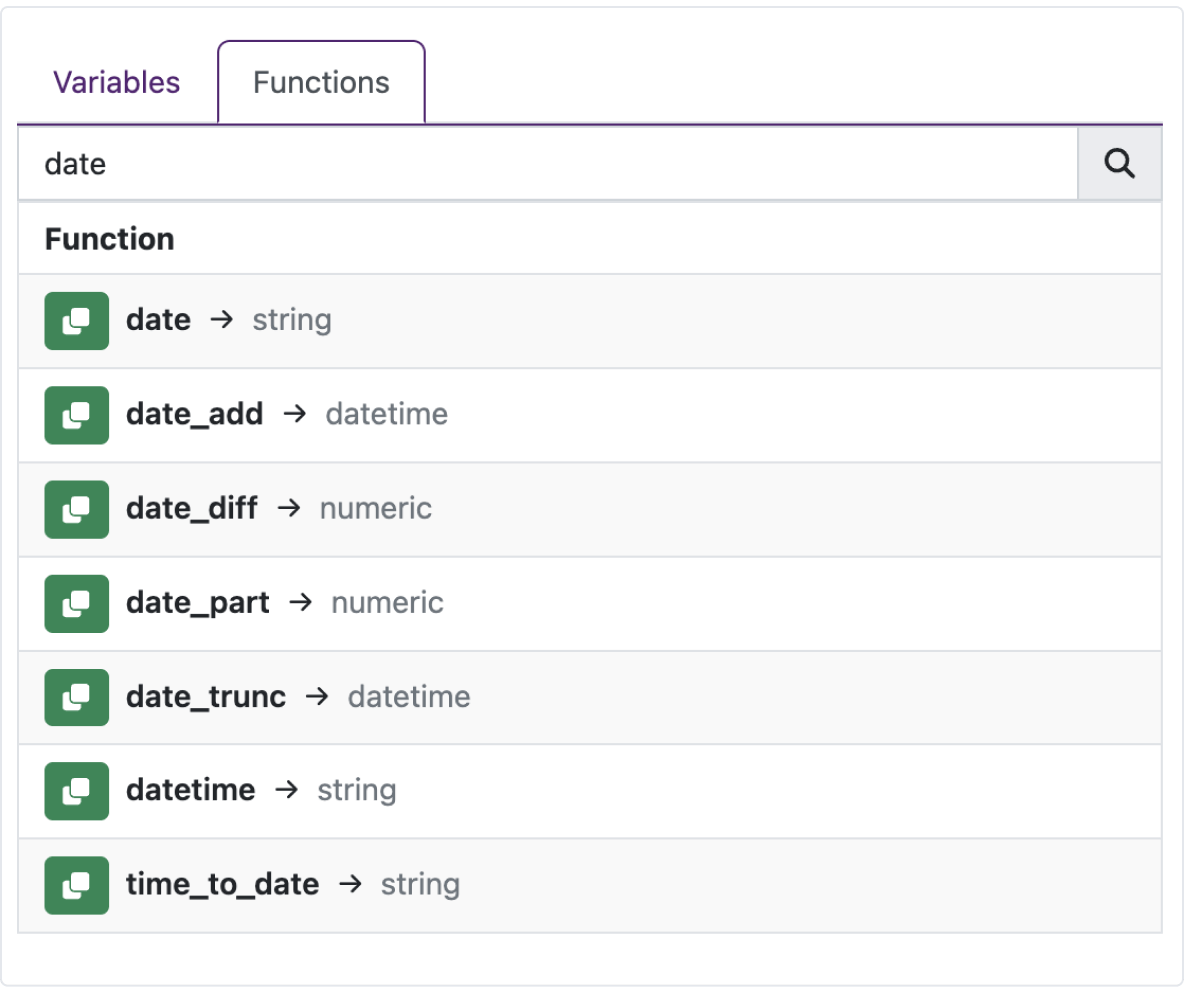
- Streamlined decision scenarios: Efficiently manage and manipulate data using equation functionality similar to Excel functions. Our system offers a comprehensive list of available equations, interactive guides, examples, and testing options.
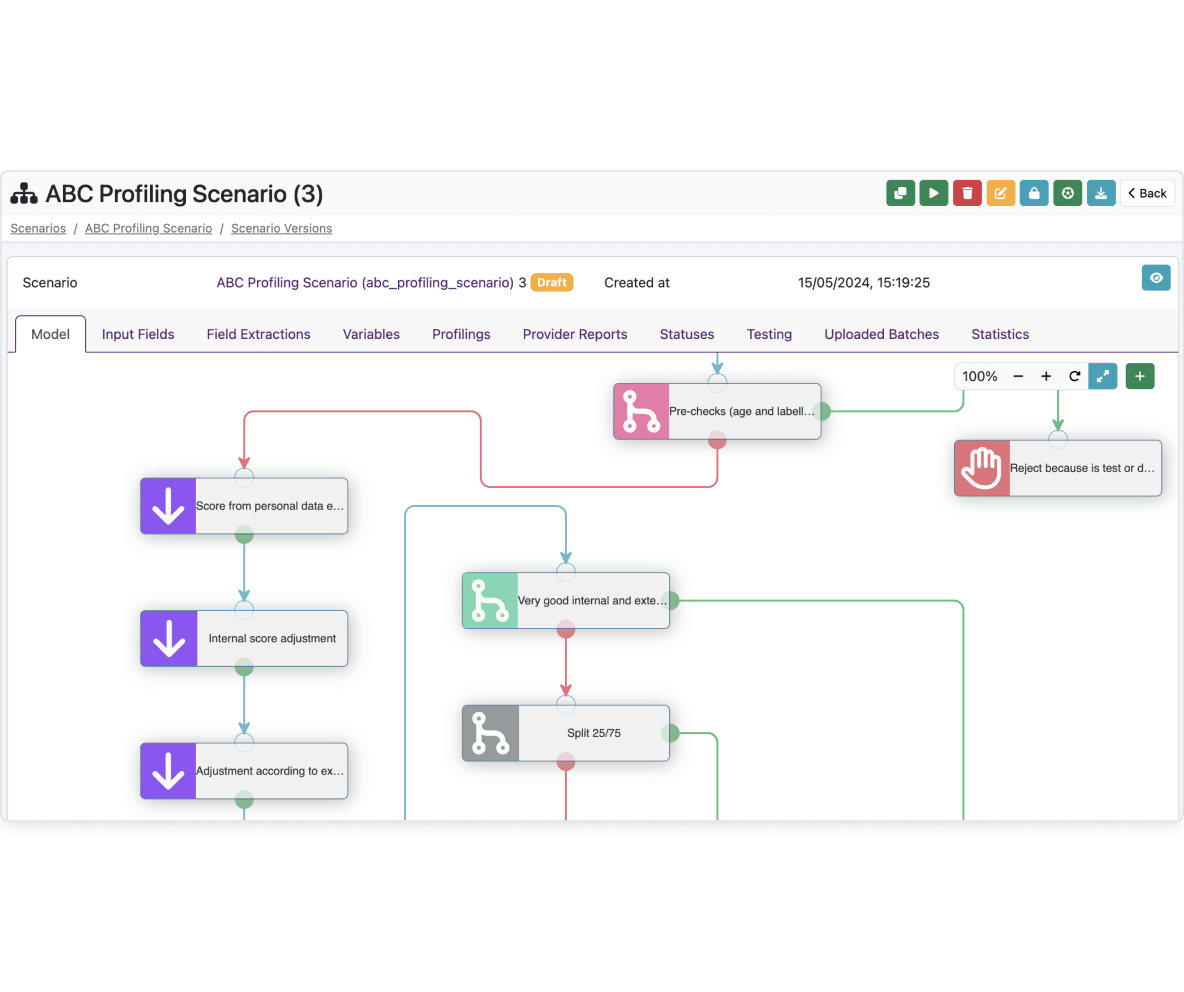
Visual modeling
Simplify the creation and management of decision-making and customer scoring models with our user-friendly credit risk management software.
- Drag-and-drop functionality: Easily change and rearrange elements by dragging and dropping them to needed places, enhancing convenience and flexibility when designing models.
- Enhanced risk evaluation and application scoring: Use the decision process to design optimal risk evaluation and application scoring tailored to your company's needs.
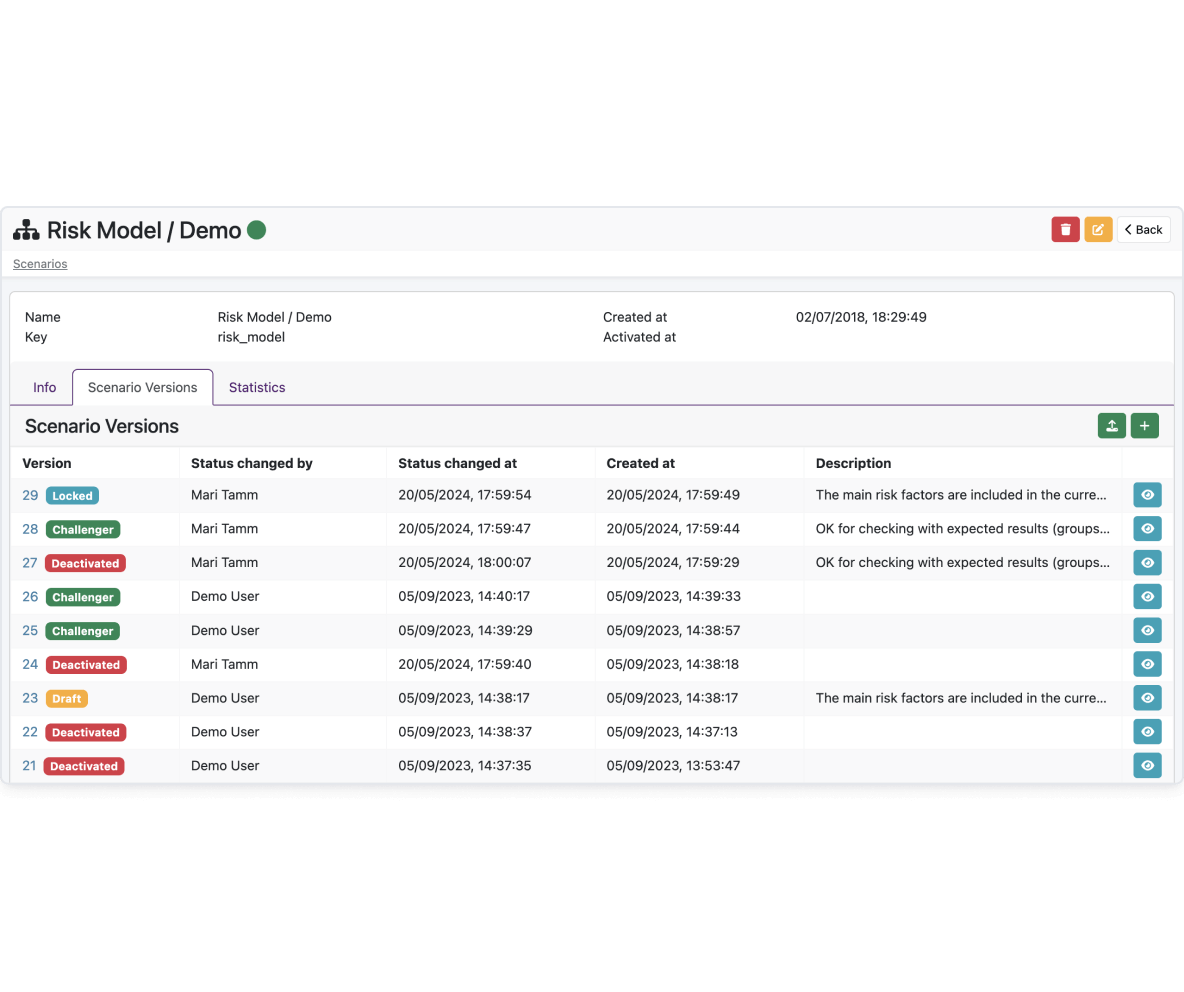
- Version control and status indicators: Maintain a clear history of model activations and deactivations, with the ability to designate a model version as a challenger or lock a prepared model. Stay informed with status signs for an easy overview of version states.
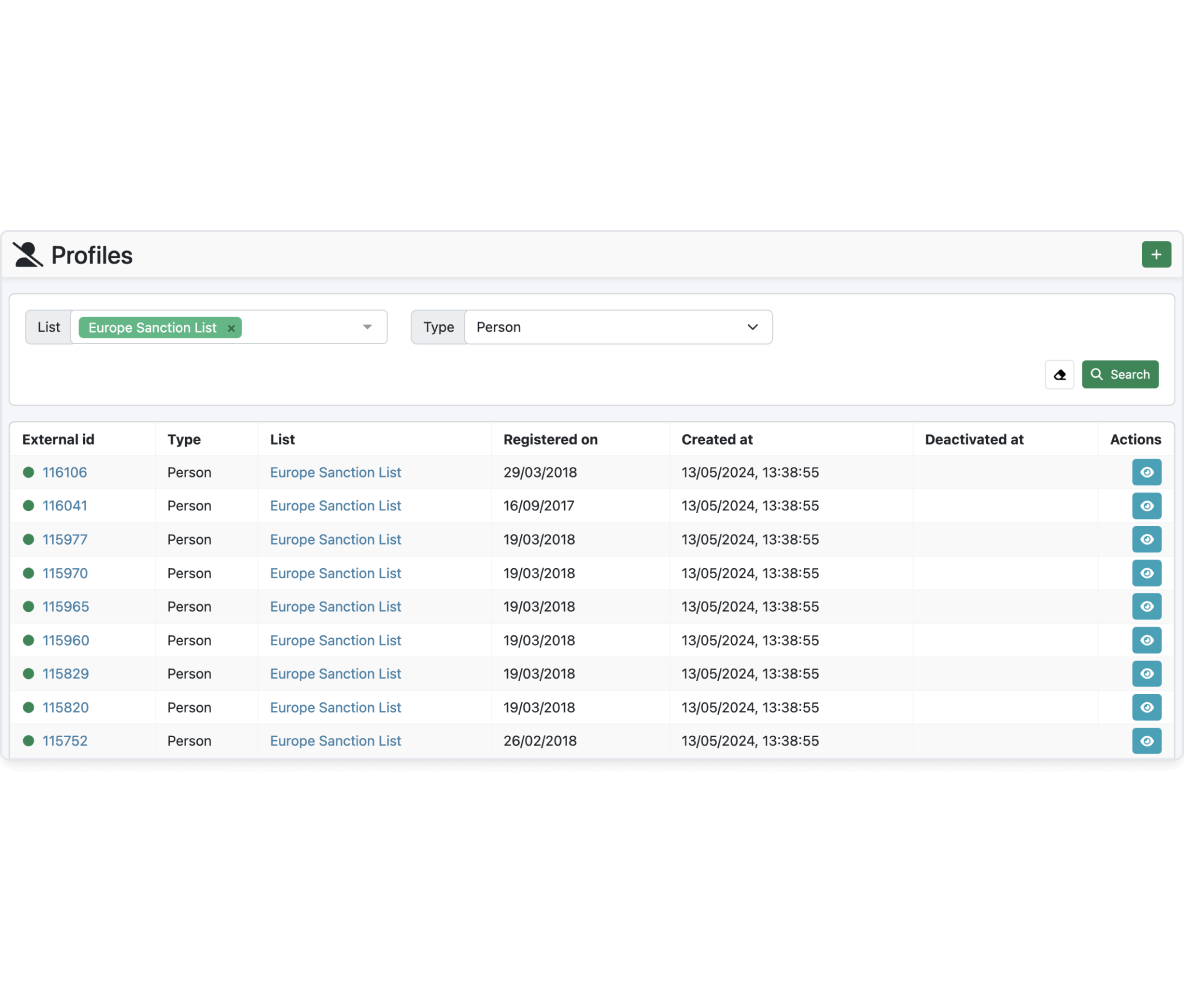
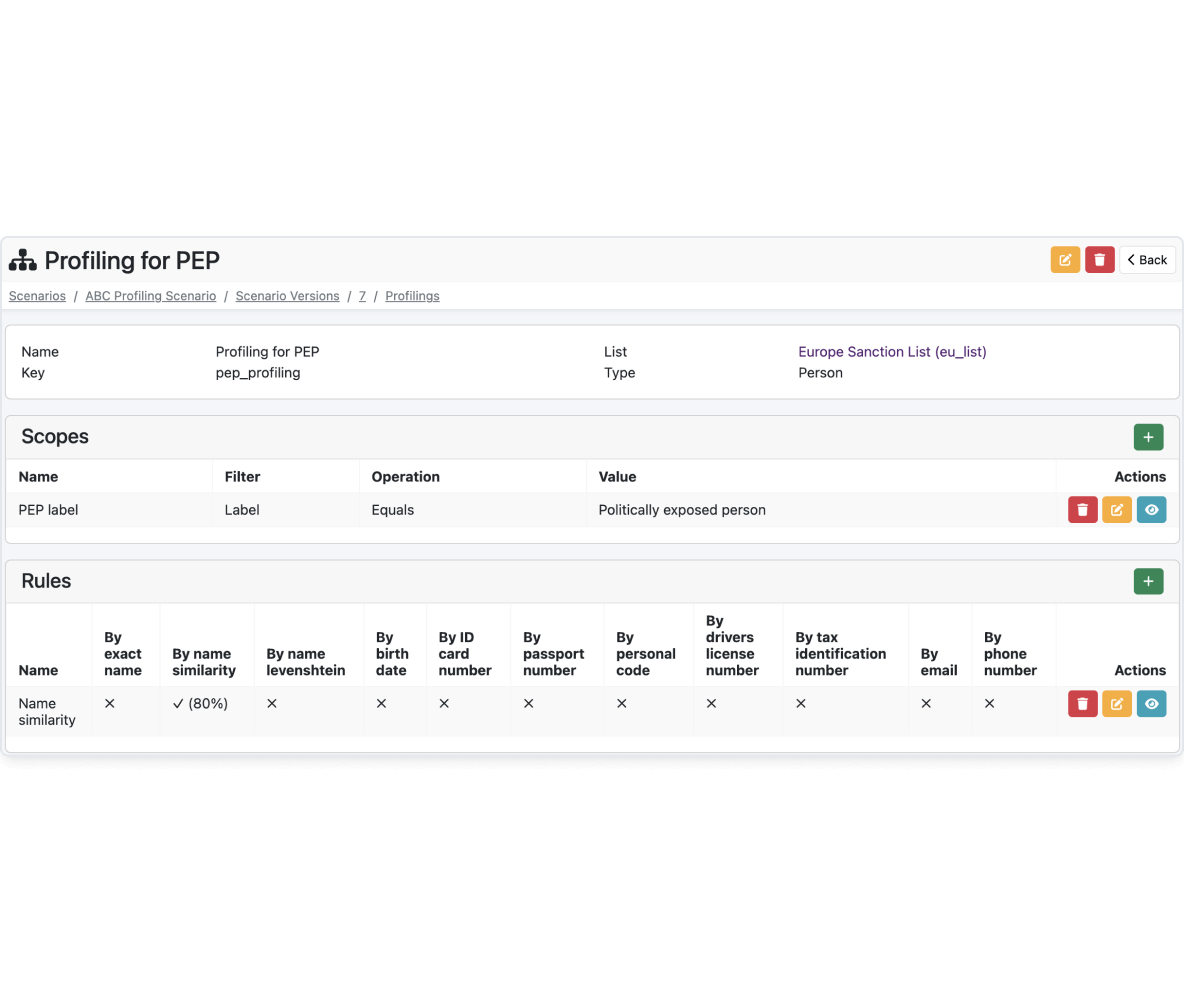
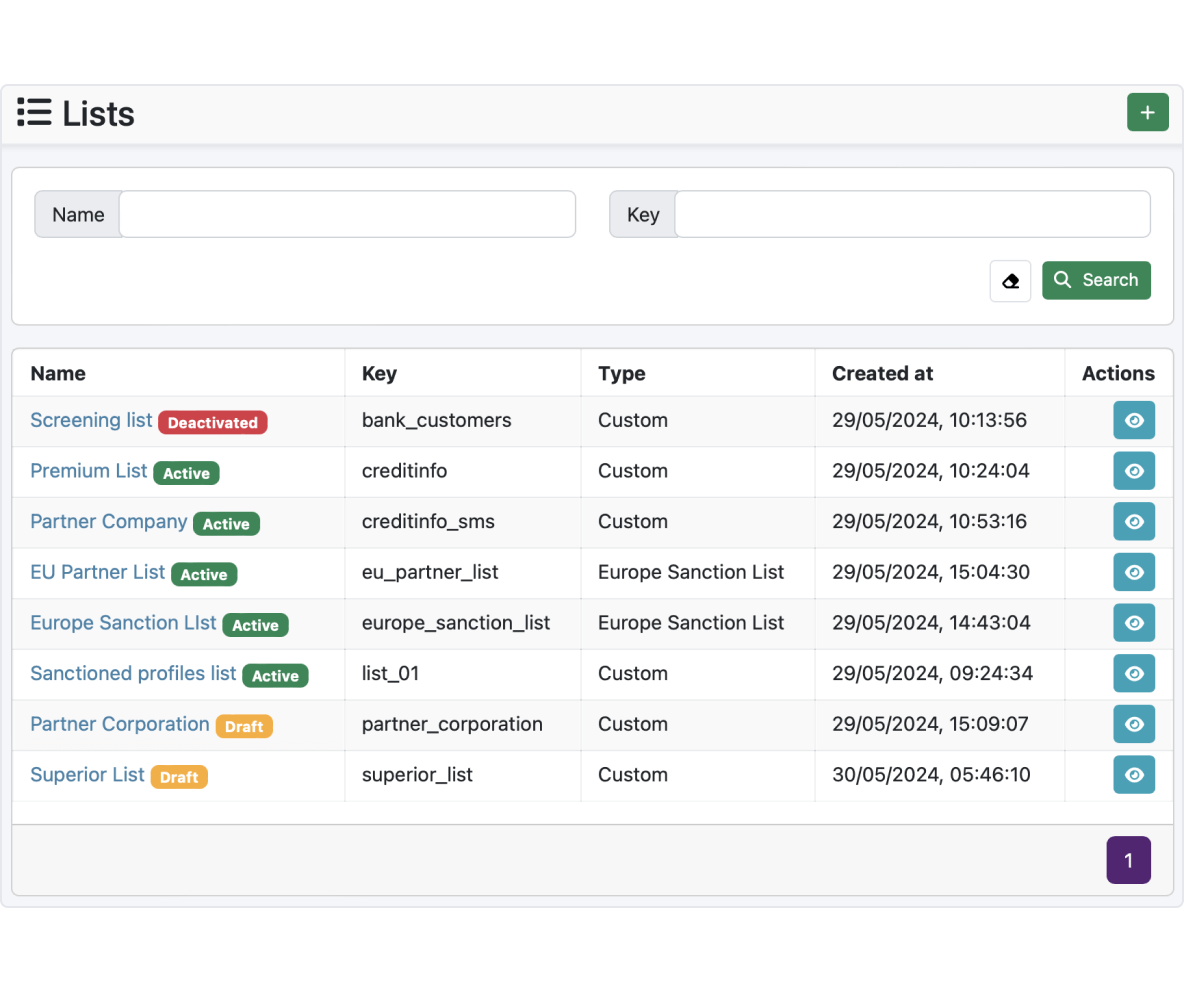
Profiling lists
Our system uses advanced profiling capabilities to match against designated lists and accurately identify high-risk entities. The customizable scopes and rules allow profiling based on specific criteria, ensuring thorough risk assessment.
- Profile management: Use demographic, behavioral, and transactional data to create detailed customer profiles for various purposes such as risk assessment, compliance checks, or targeted marketing.
- Profiling: Scenario-based profiling enables organizations to compare lists and identify matches based on set criteria, such as politically exposed persons (PEPs) using various identification methods.
- Integrated and custom lists: Our solution enables screening against global lists or creating custom lists containing individuals or companies. Specific profiles relevant to your organization's risk management strategies can be imported into the custom list.
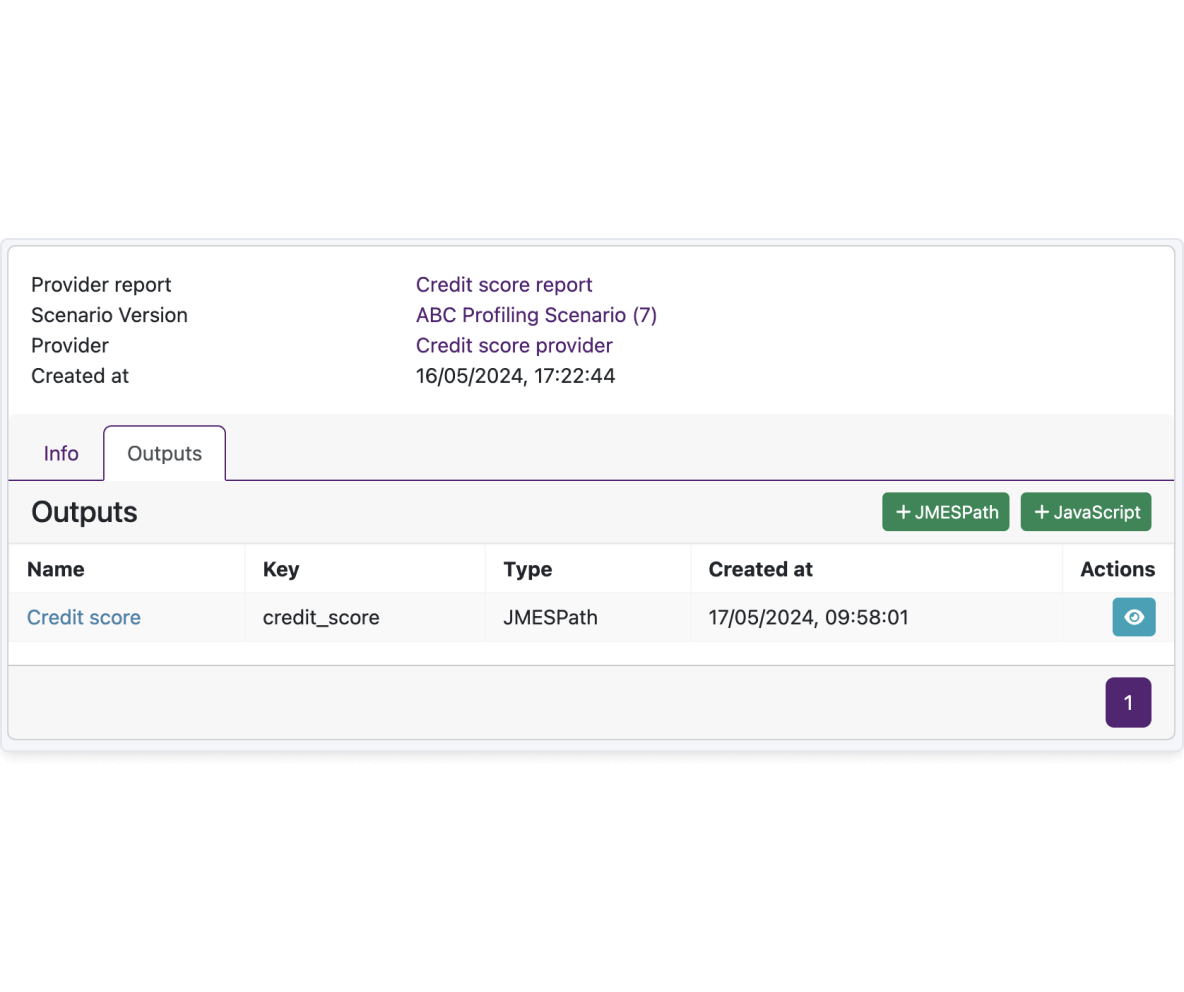
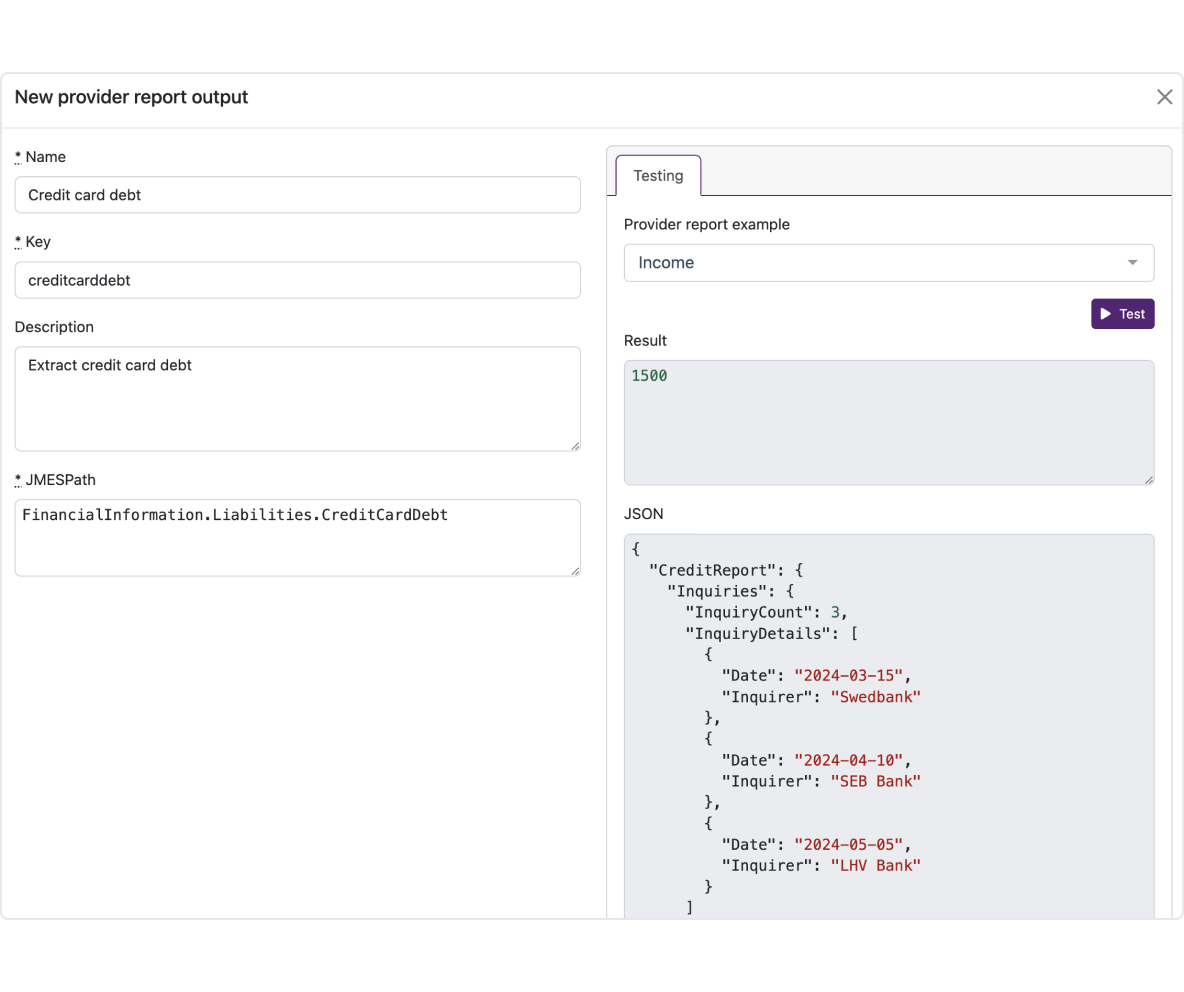
Provider reports
Receiving and combining data from various providers helps businesses understand customer behavior and comply with the law.
- Integrated systems: Introducing a process for setting up and managing external integrations within the system. This includes steps for adding providers, reports, examples, cache settings, and testing functionalities.
- Unified data structure: Our solution integrates different providers to collect, store, and use data for customer evaluations and their behavior in compliance with legal requirements. All collected data is formatted into a unified structure, ensuring compliance with data protection regulations.
- Data utilization in models: High-level data integrity, compliance, and operational efficiency lead to better-informed decision-making and improved risk management outcomes. Incorporating provider reports into a decision model allows you to leverage output fields to extract the data required for informed decision-making.
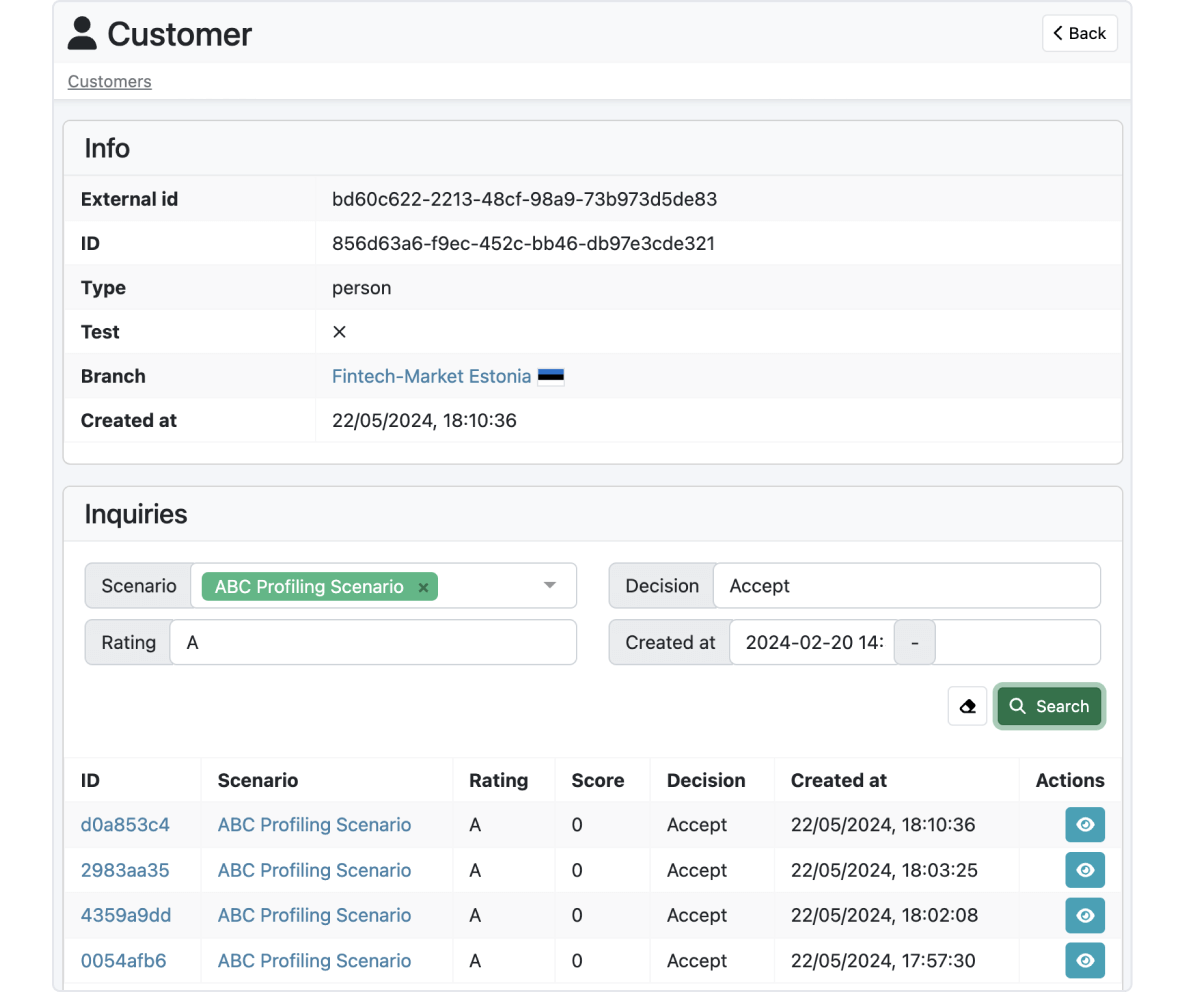
Visual analysis and testing
Effortlessly configure your risk model on FTM credit risk management software and verify its performance with our comprehensive testing functionality.
- Versatile testing capabilities: Utilize the testing tool to ensure the proper functioning of your risk model. Test already active scenario versions manually or via API to validate the results.
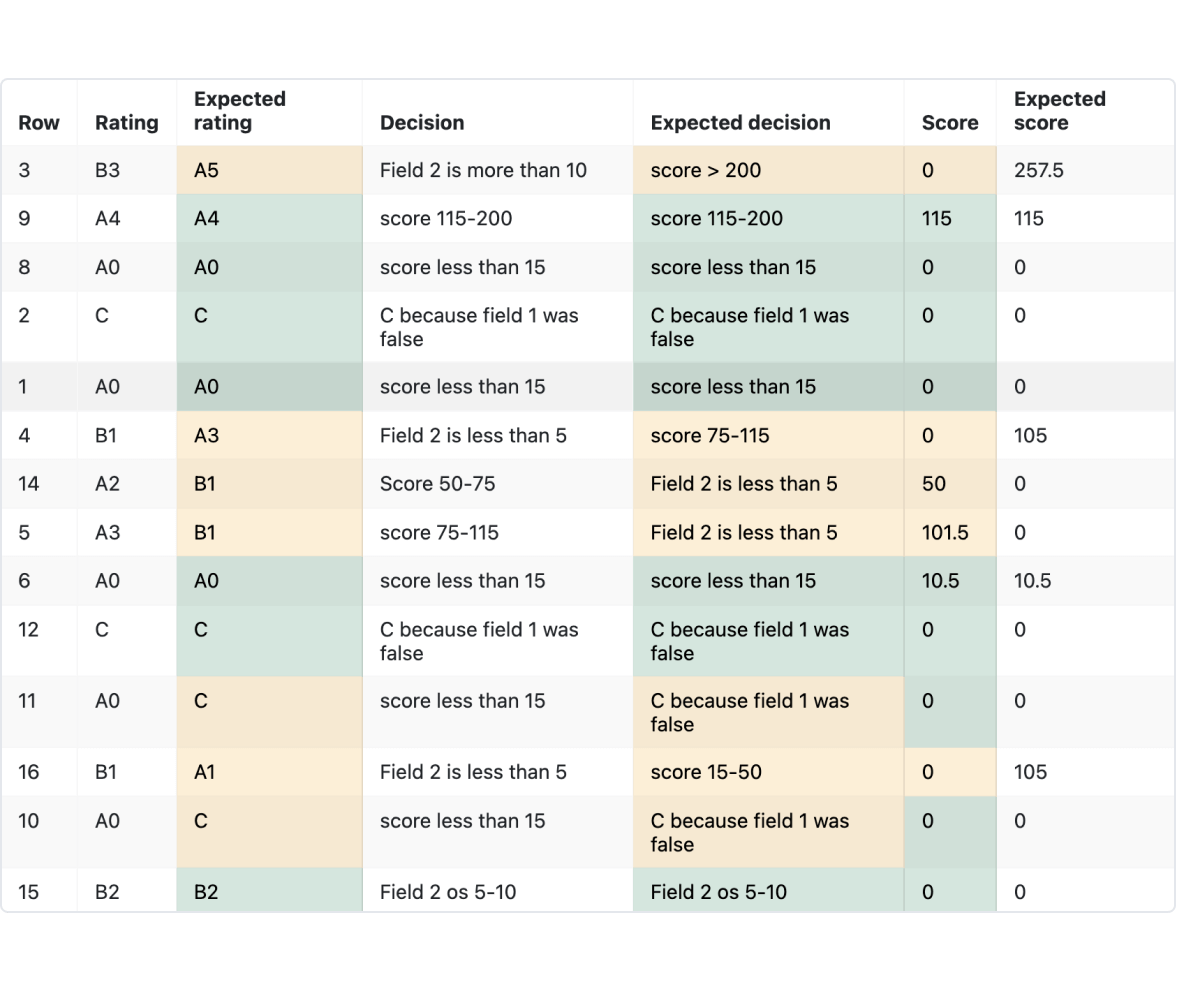
- Batch testing: Enhance decision-making with the batch testing option, that allows to test and analyze a large amount of data with the possibility to compare expected results.
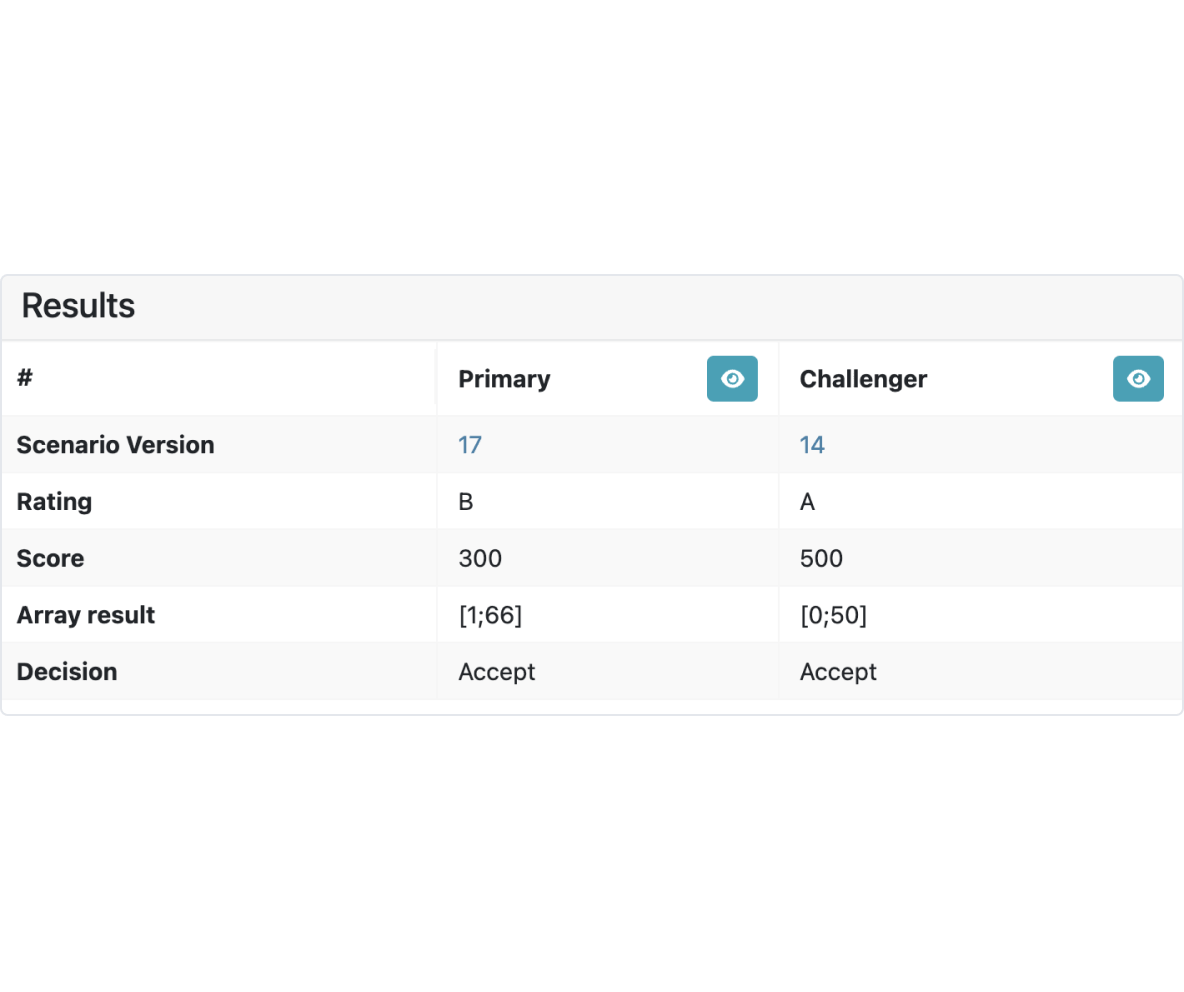
- Decision strategy comparison: Leverage the Champion Challenger testing to evaluate and identify the best-performing decision strategies. The A/B testing option is there to get the fastest results based on the customer's real behavior.
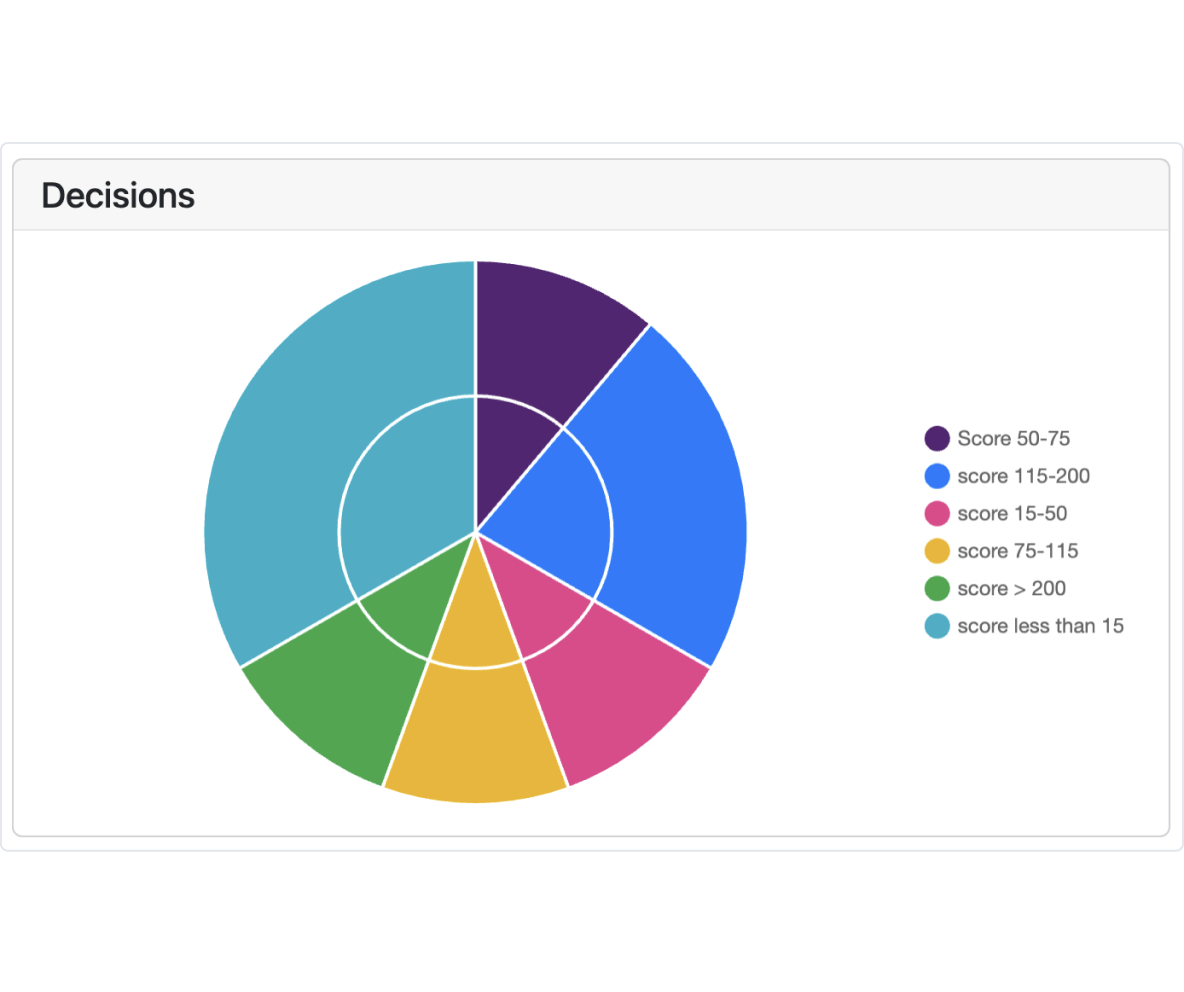
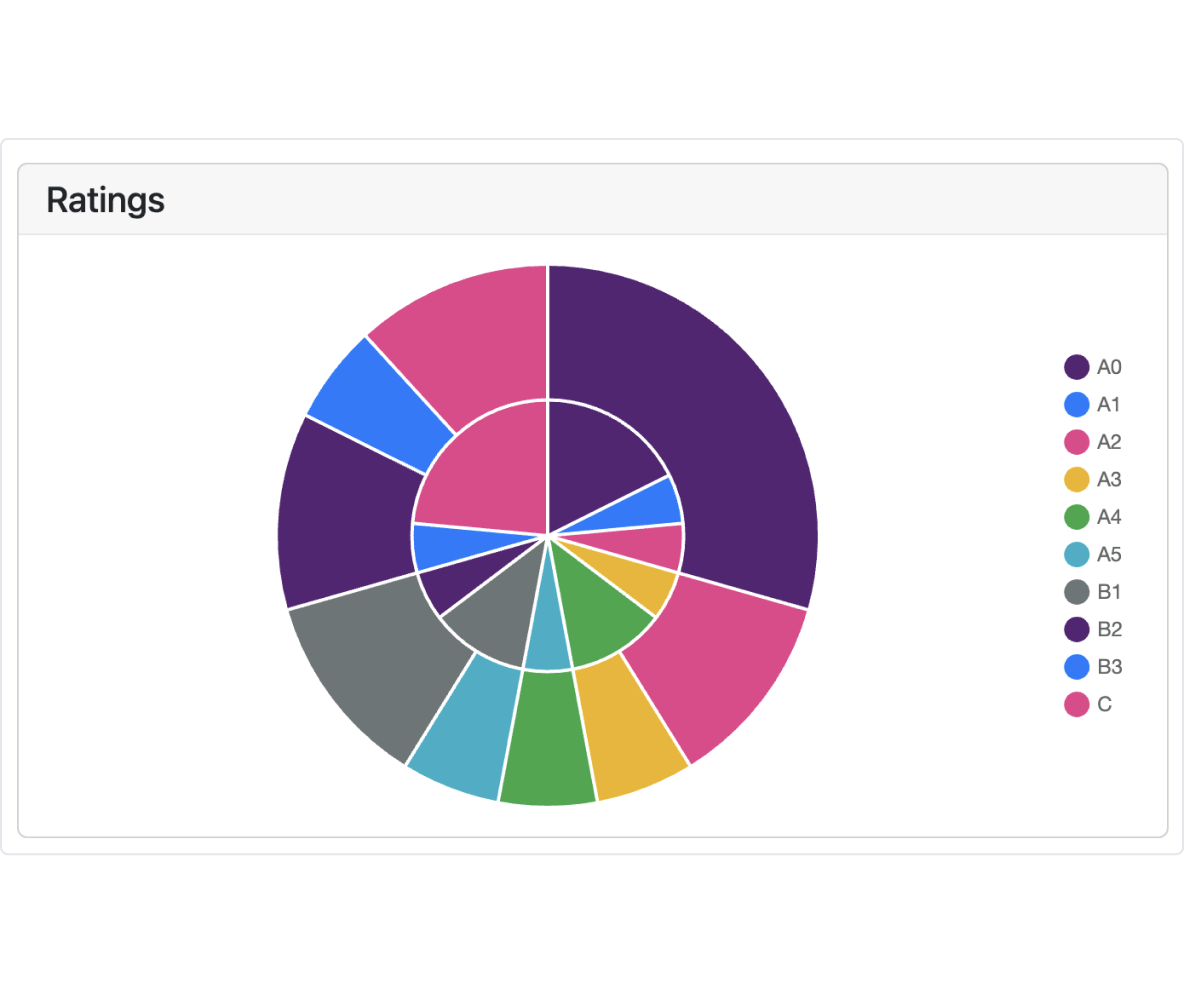
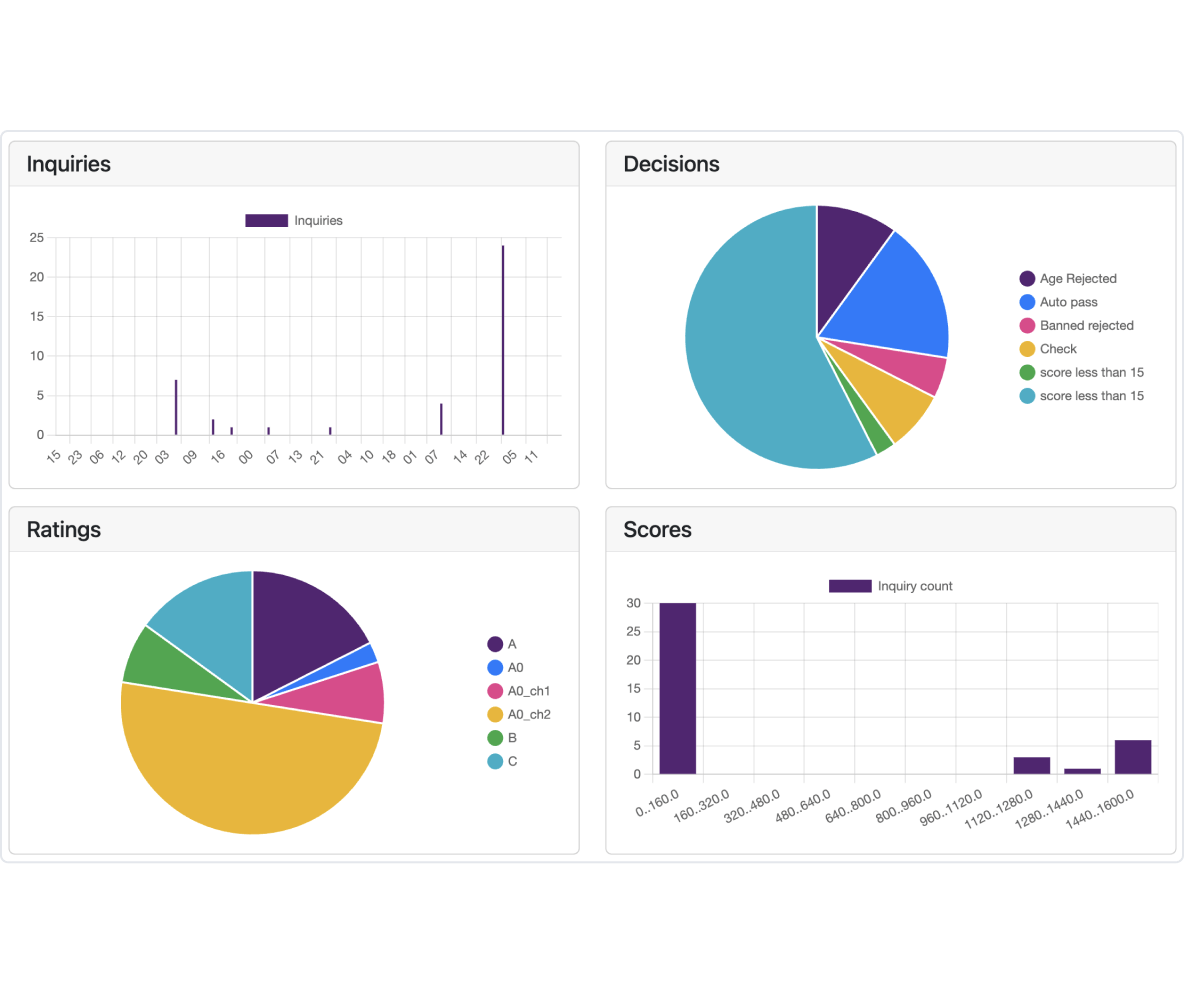
Statistics and distribution
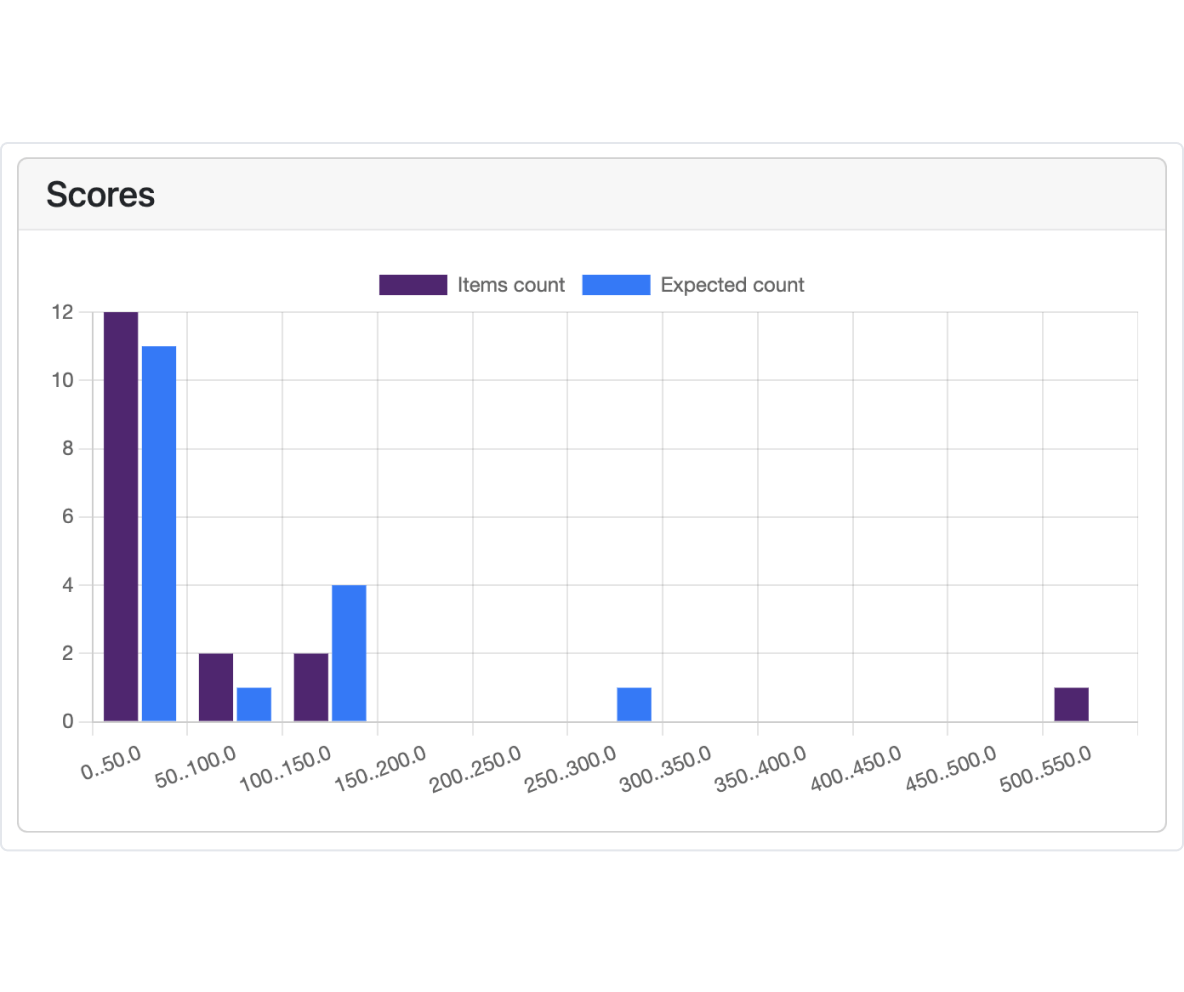
Our application gives comprehensive real-time insights and visualization of your risk model inquiries.
- Graphical representation: Obtain a clear understanding of inquiries through visually appealing graphs, providing a concise summary.
- Version-specific and scenario results: Easily access specific version results or general scenario results as required.
- Detailed information and model comparison: Retrieve in-depth information about each request, including the results summary and distribution of decisions, ratings, and scores used with the model and its versions, including a comparison of alternative models, if the Champion Challenger option is used.
Do you want to explore all features?
Our team would be delighted to introduce you to all the functionalities. Schedule a demo to explore how our solution aligns with your business needs.